AJAYI BOLUWATIFE
Information Security & Offensive Operations
SIEM engineer, red team practitioner, and automation builder. I deliver measurable risk reduction through detection engineering and adversarial simulations.
┌──(boluwatife㉿portfolio)-[~/security]
└─$ nmap -sV --script vuln enterprise-siem.lab
└─$ nmap -sV --script vuln enterprise-siem.lab
~/Reconnaissance
profile
Offensive security engineer with deep focus on SIEM engineering, purple team exercises, and security automation. I build detection pipelines, simulate real-world attacks, and help organizations mature their security posture.
eJPT eLearnSecurity (in progress)
Splunk Core User
CompTIA Security+ (in progress)
AZ-900 (in progress)
TryHackMe Top 50%
core philosophy
Every attack simulation improves detection logic. I build for resilience, not compliance. real world testing drives measurable defense improvements.
$ whoami
> Ajayi Boluwatife · Offensive Security · SIEM Architect
> Ajayi Boluwatife · Offensive Security · SIEM Architect
~/Exploits
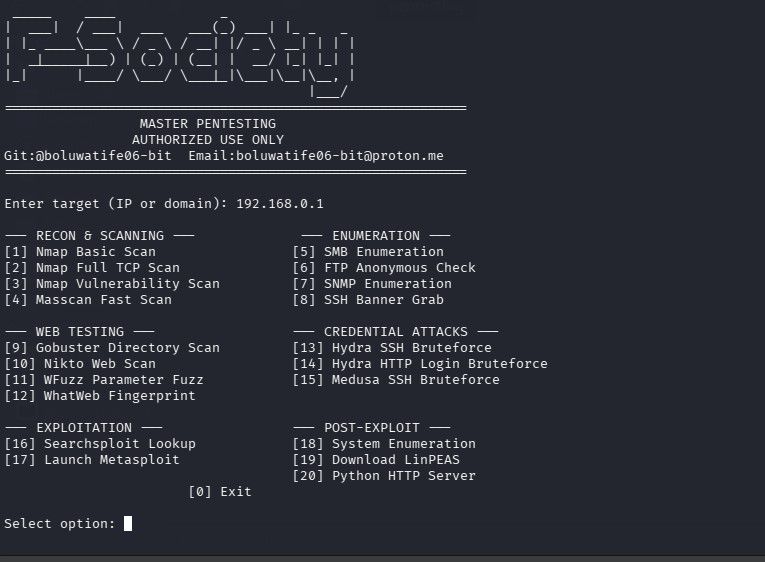
Master Pentesting Framework
PythonBashNmapHydra
Modular pentesting automation suite with recon, enumeration, web testing, credential attacks, and post‑exploitation modules. Designed for authorized red‑team exercises.
$ ./master-pentest --target 192.168.0.1 --scan full
- 15+ integrated tools (Nmap, Gobuster, Hydra, Metasploit)
- Used in internal penetration tests & CTFs
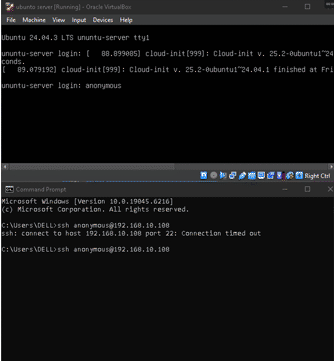
SSH brute force simulation
HydraMetasploitLog Analysis
Simulated credential stuffing against Ubuntu lab server, analyzed auth logs, deployed rate-limiting and IDS alerts.
$ hydra -l root -P rockyou.txt ssh://target.lab
- Improved detection rules for authentication anomalies

web app penetration test
Burp SuiteZAPSQLmap
Detected SQLi, XSS, clickjacking on live staging apps. Collaborated with developers on remediation.
- Delivered executive & technical reports with PoC
AI vulnerability scanner
PythonScikit-learn
ML-based anomaly detection on HTTP requests — reduced false positives by 40%.
- Integrated into CI pipeline for proactive scanning
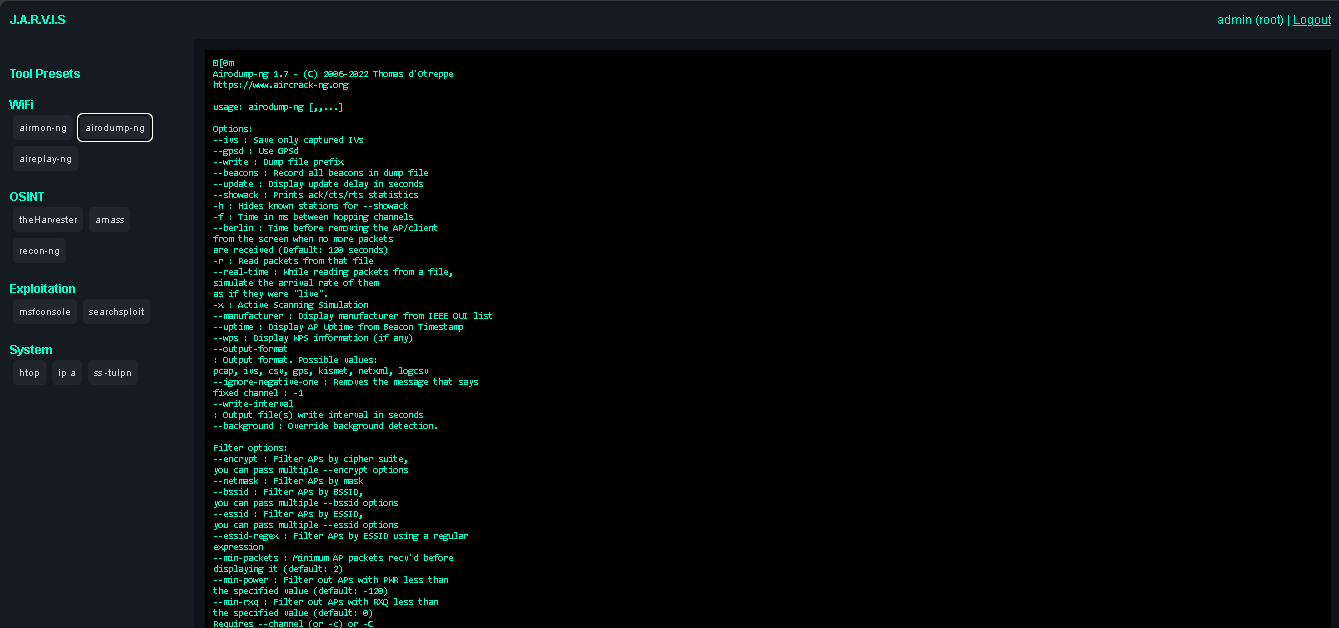
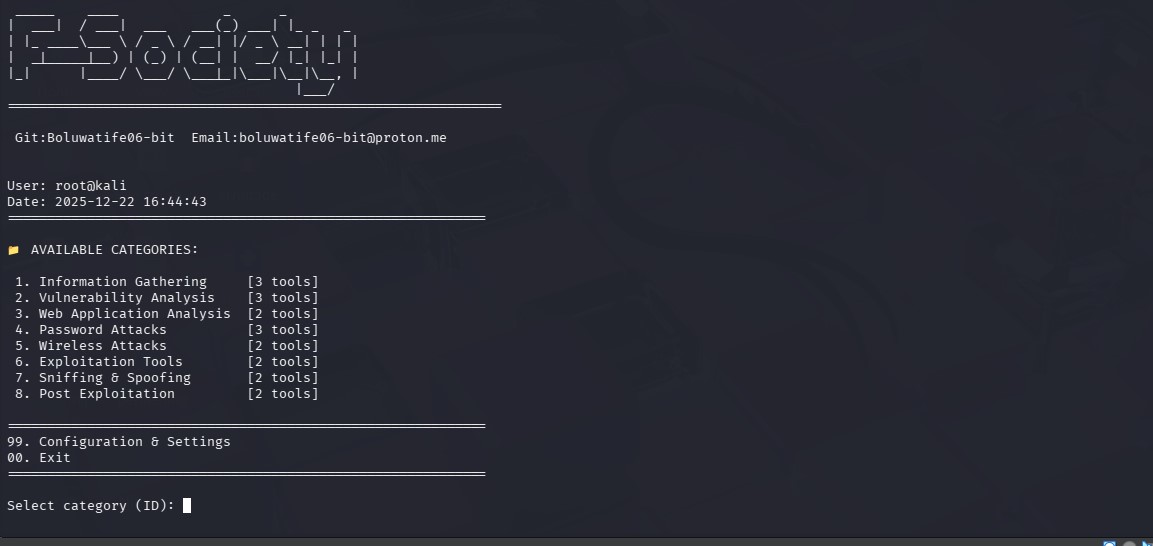
J.A.R.V.I.S AI terminal
Kali LinuxNLPBash
AI assistant for pentesting: natural language → Nmap, gobuster, reverse-shell generation.
- Accelerated reconnaissance & reporting
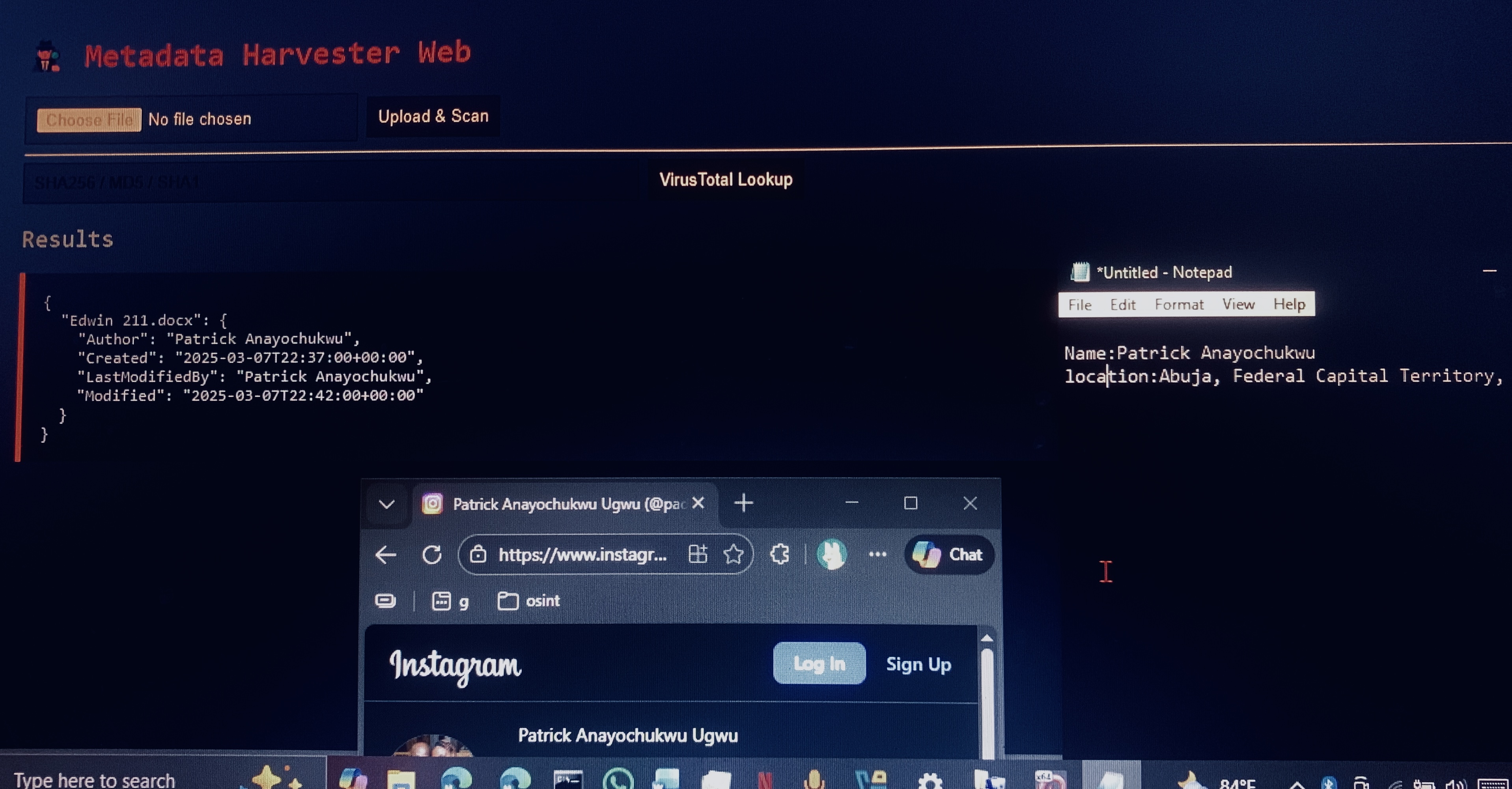
metadata harvester
ExifToolPythonOSINT
Forensic extraction of GPS, authors, hidden data from images/PDFs/Office docs.
- Used in red-team OSINT & data leakage audits
~/Defense
enterprise SIEM lab
SplunkELKSysmonSigma
Production-grade SIEM with correlation rules, MITRE ATT&CK mapping, real-time dashboards. 50k+ EPS ingestion.
- 38% faster incident detection
- Automated alerts for anomalous PowerShell
network defense & IDS
SnortWiresharkpfSenseVLAN
Deep packet inspection, custom Snort rules, zero-trust segmentation. Uncovered plaintext creds.
- 25% reduction in false positives
- Deployed network honeypot
vulnerability management
NessusBurp SuiteMetasploit
Full-cycle vuln assessment, exploitation, remediation reports. CVSS v3.1 prioritization.
- 70% reduction in critical vulns
- 15+ professional reports
security automation
PythonBashThreat Intel APIs
Log parser for malicious IPs + OTX enrichment. CIS Level 1 Linux hardening script.
- Automated weekly vuln reports
- Containerized scanner with Trivy
ubuntu server hardening
UFWFail2BanSSH Hardening
CIS Level 1, Cloudflare Tunnel, intrusion prevention. Reduced attack surface by 63%.
$ sudo ufw enable && fail2ban-client status sshd
- Achieved compliance benchmark
SOC analysis lab
WazuhElasticsearchFilebeat
Centralized logging, custom decoders for SSH brute-force, MITRE ATT&CK mapping.
- Real-time Kibana dashboards & alerting
~/Tools
~/Contact
SIEM architect, red team operator, automation engineer — open to senior security roles.
boluwatife06-bit@proton.me